@david-cuen OK, I was able to get more than 10, but you're right about it possibly being the size. Is it possible for you to share the theme you are using with us or me individually? I don't want you to give away any secrets, proprietary info or share anything private if you can't but getting a look at the theme may help.
FAQ Posters
Users who have rights to post in the FAQ category.
-
RE: Admin UI actions over themes blocks application since 1.61.2posted in General Discussion
-
RE: can't use fusion auth react sdk when fusion auth server runs locally on fusionauth.localhost:posted in Q&A
@bernardo-munz Did you play with the SameSite setting?
-
RE: Admin UI actions over themes blocks application since 1.61.2posted in General Discussion
@david-cuen Awesome that you have isolated the issues. I am going to test from my side and see if I can replicate with the 10+ themes. If I can then you should report this as a bug. I will let you know what I find. Hope to be able to get to this today.
-
RE: Admin UI actions over themes blocks application since 1.61.2posted in General Discussion
@david-cuen can you try to spin up a new instance and let me know if you see the problem? If not, it may have to do specifically with the themes themselves. If the new instance works correctly, import each theme and test. This may help narrow the issue.
-
RE: Admin UI actions over themes blocks application since 1.61.2posted in General Discussion
@david-cuen Thanks for the detailed message. I hope to have some time today to try and replicate this. I will let you know what I see.
-
RE: oauthConfiguration.clientSecret is missing on /api/application/search response since 1.62.0posted in Q&A
@simon-chrzanowski can you please share the code you using? (please be sure to hide anything sensitive like your API Key)
-
RE: Pass value from API to webhookposted in Q&A
@alexandros-nafas , were you able to figure it out?
-
RE: Pass value from API to webhookposted in Q&A
@alexandros-nafas are you trying to make an update through the API then reflect that value of are you trying to pass a value in the URL and get that? It may help to give an example.
-
RE: retrieve_user_using_jwt is not working with FA 1.62.1posted in Q&A
@johnmiller It looks like the issue is that the 'retrieve a user via JWT' functionality was removed in 1.60.0. (It appears the User API JWT authentication method was deprecated in version 1.50.0. An issue has been filed to remove it from the client libraries.
Thank you from bringing this to light.
-
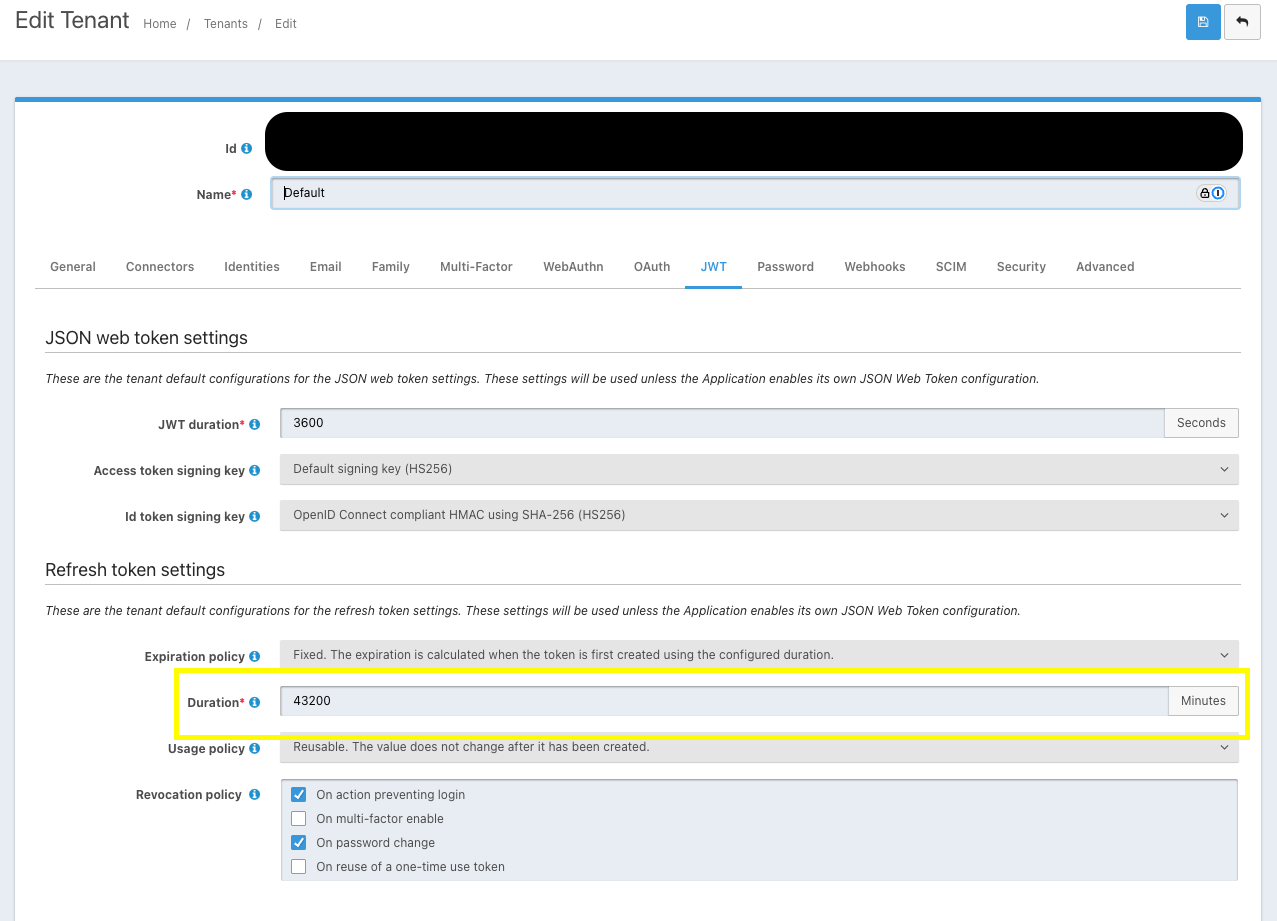
RE: How can I configure session timeout on the admin panel?posted in Q&A
@rachel-flatt OK, it looks like your application is using the JWT setttings from the Tenant. You can go to the Admin UI select Tenants -> Find the tenant your application is under -> Select Edit and go to the JWT tab. You should find the settings there.